[2 min. read]
Cybersecurity and Ostrich-itis
When it comes to knowing what your company’s security vulnerability status is, if you’re not looking,
everything probably looks perfect. It might sound obvious, but after reading Checkpoint’s yearly security
report for 2022, it looks like vulnerabilities aren’t being remediated which could mean, companies aren’t
even aware of their own organizational risk.
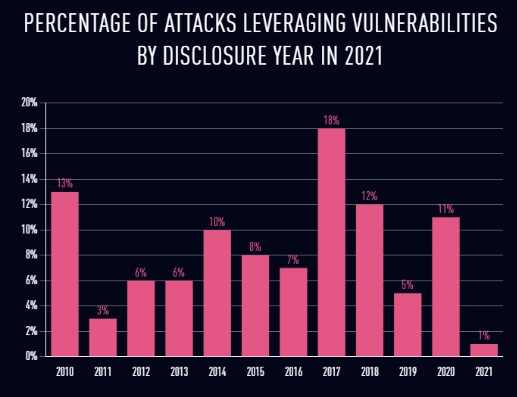
The following graph shows that 83 percent of attacks in 2021 used vulnerabilities that were at least two
years old with 42 percent being over 7 years old.
Why Cyber Insurance Needs Vulnerability Assessments
Either these vulnerabilities are being ignored, the risk accepted, or companies aren’t scanning for vulnerabilities that would pinpoint these for remediation. Perhaps the belief that it will never happen to us because we are too small of a target and don’t have anything of value. The problem with this thought process is that you are putting your entire company at risk. Should a breach of confidential data occur, or loss of system resources cause you to have your computer systems go offline this may put your organization unable to access technical resources.
In the past, this risk has been reduced through the ability to transfer this risk to Insurance companies. It seems that this is now changing as Insurance companies are requiring best practices to be implemented before Cyber Insurance policies are finalized. This may include a requirement for a vulnerability assessment to be completed that detail the vulnerabilities within your organization. This will allow you to be aware of risks to the organization.
Vulnerability Assessments & Management from Morefield
At Morefield, we provide vulnerability scans to organizations which include an initial vulnerability scan, providing various reports to allow remediation by the company, and a follow-up scan that shows remaining vulnerabilities left after remediation. We recommend that security patches are applied to systems and software to minimize exposed vulnerabilities and to minimize the possibility that defenses are penetrated. We support cybersecurity framework guidelines that recommend remediation for critical vulnerabilities within 30 days and high vulnerabilities within 60 days.
If you find yourself requiring a vulnerability scan to obtain cyber insurance, we can assist you in providing the information you need and work with you to prioritize remediation to fulfill the requirements for cyber insurance.
We also offer a vulnerability management solution to allow monthly scans to be completed and we work with the organization to discover, prioritize, assess, assist with remediation, verify, and report vulnerabilities.
Contact our team of experts today!
written by: Allan Jacks, vCISO (Virtual Chief Information Security Officer)