6 Things You Should Do to Handle Data Privacy Updates
Data Backup Is Not Enough, You Also Need Data Protection
The need to back up data has been around since floppy disks. Data loss happens due to viruses, hard drive crashes, and other mishaps. Most people using any type of technology have experienced data loss at least once.
There are about 140,000 hard drive crashes in the US weekly. Every five years, 20% of SMBs suffer data loss due to a major disaster. This has helped to drive a robust cloud backup market that continues to grow.
But one thing that’s changed with data backup in the last few years is security. Simply backing up data so you don’t lose it, isn’t enough anymore. Backing up has morphed into data protection.
What does this mean?
It means that backups need more cybersecurity protection. They face threats such as sleeper ransomware and supply chain attacks. Cloud-based backup has the benefit of being convenient, accessible, and effective. But there is also a need for certain security considerations with an online service.
Companies need to consider data protection when planning a backup and recovery strategy. The tools used need to protect against the growing number of threats.
Some of the modern threats to data backups include:
• Data Center Outage: The “cloud” basically means data on a server. That server is internet accessible. Those servers can crash. Data centers holding the servers can also have outages.
• Sleeper Ransomware: This type of ransomware stays silent after infecting a device. The goal is to have it infect all backups. Then, when it’s activated, the victim doesn’t have a clean backup to restore.
• Supply Chain Attacks: Supply chain attacks have been growing. They include attacks on cloud vendors that companies use. Those vendors suffer a cyberattack that then spreads throughout their clients.
• Misconfiguration: Misconfiguration of security settings can be a problem. It can allow attackers to gain access to cloud storage. Those attackers can then download and delete files as they like.
What to Look for in a Data Protection Backup System
Just backing up data isn’t enough. You need to make sure the application you use provides adequate data protection. Here are some of the things to look for when reviewing a backup solution.
Ransomware Prevention
Ransomware can spread throughout a network to infect any data that exists. This includes data on computers, servers, and mobile devices. It also includes data in cloud platforms syncing with those devices.
95% of ransomware attacks also try to infect data backup systems.
It’s important that any data backup solution you use have protection from ransomware. This type of feature restricts automated file changes that can happen to documents.
Continuous Data Protection
Continuous data protection is a feature that will back up files as users make changes. This differs from systems that back up on a schedule, such as once per day.
Continuous data protection ensures that the system captures the latest file changes. This mitigates data loss that can occur if a system crashes before the next backup. With the speed of data generation these days, losing a day’s worth of data can be very costly.
Threat Identification
Data protection incorporates proactive measures to protect files. Look for threat identification functions in a backup service. Threat identification is a type of malware and virus prevention tool.
It looks for malware in new and existing backups. This helps stop sleeper ransomware and similar malware from infecting all backups.
Zero-Trust Tactics
Cybersecurity professionals around the world promote zero-trust security measures. This includes measures such as multi-factor authentication and application safelisting.
A zero-trust approach holds that all users and applications need ongoing authentication. So, just because a user is logged into the system today, doesn’t mean they are completely trusted.
Some of the zero-trust features to look for include:
• Multi-factor authentication
• Distinct file and folder permissions
• Contextual authentication
• Verification of permissions for file changes
Backup Redundancy
If you back up to a USB drive or CD, you have one copy of those files. If something happens to that copy, you could experience data loss.
Cloud backup providers should have backup redundancy in place. This means that the server holding your data mirrors that data to another server. This prevents data loss in the case of a server crash, natural disaster, or cyberattack.
Air Gapping for More Sensitive Data
Air gapping is a system that keeps a copy of your data offline or separated in another way. This would entail making a second backup copy of your data. Then, putting it on another server. A server disconnected from external sources.
This is a feature that you may want to seek out if you deal with highly sensitive data. It helps to ensure that you have at least one other copy of your backup. A copy walled off from common internet-based attacks.
Need Help With Secure Backup & Data Protection Solutions?
Have you updated your backup process for today’s threats? Give us a call today to schedule a chat about data backup and protection.
Article used with permission from The Technology Press.
IT Security Checklist

There’s no shortage of opportunities for small- and medium-sized businesses (SMBs) to tighten their IT security infrastructure — and no lack of reasons they should.
Only 35 percent of Chief Information Security Officers surveyed this year said they were comfortable with their organization’s ability to identify, contain and correct a security compromise. Nearly 30 percent also said they suffered from “cyber-fatigue,” the hamster-wheel exhaustion of responding to the seemingly mounting list of cybersecurity threats while still feeling exposed.
With IT departments so often siloed, security best practices must balance users, networks, data, apps and endpoints. It’s no small undertaking, but it’s essential in guarding an organization’s reputation.
We’ve compiled what should be on an IT security checklist for small businesses — the core practices moving IT teams off the hamster wheel and into proactive, not reactive, IT enterprise security.
Business IT Security Checklist: What Are the Top Network Security Concerns Facing Organizations?
Business IT security checklists aim to address these top malicious cybersecurity incidents and attacks before they become mission-critical, non-recoverable breaches.
1. Malware
Downloading malicious software is one of the most common user behaviors at fault for enterprise data loss and system attacks. Malware wreaks havoc when users mistake computer apps, programs, links, files or entire websites as their benign versions. In reality, these applications are corruptions, designed to look and even act like the real thing. Employees, unaware of all this, then conduct regular activity on or through these programs, providing an opening for the malware to infect desktops, laptops, mobile devices and even the entire network.
2. Phishing Schemes
Phishing schemes target organizations via email. They attempt to mimic important organizational stakeholders — upper management, other team members, business vendors, etc. — to elicit sensitive or personal information. Employees untrained or not fluent in identifying phishing red flags pose a severe threat to enterprise data and access control security.
3. Spyware
Spyware is a type of malware specifically designed to enter devices and track internet usage, account usernames and passwords. Cybercriminals use the information gleaned from tracking to hack business accounts or pose as prominent organization members, often to extract further sensitive enterprise data.
4. Ransomware
Ransomware takes extortion tactics digital. Entering a network through traditional malware — clicked links, downloadable attachments, newly installed software, etc. — ransomware can shut down or block access to essential files or systems until an organization pays a ransom or hands over demanded data.
5. Mobile Malware
Mobile malware are a type of malware virus-coded to infect mobile devices such as smartphones, tablets and tech wearables. This IT threat continues to mount as more and more organizations grow lenient with their bring-your-own-device (BYOD) policies yet increase their dependency on mobile- or remote-device infrastructure. Plus, with the inevitability of the Internet of Things, mobile devices pose a higher security risk in their very interconnected nature — even for businesses with thorough network and device defenses.
6. Improper File Sharing
While not a cybersecurity threat in the traditional sense, business network leaders have identified careless file sharing as a core concern underpinning several of the direct attack categories above. Many organizations struggle to standardize acceptable use policies or internet access policies, which are meant to curb file-sharing and file-access risks — if they have these policies at all.

What Are IT Security Best Practices?
While there are numerous approaches to small business network security best practices, their guiding philosophy remains the same: Institutionalize a series of practical, everyday activities and technologies that position a business to identify and handle cybersecurity threats in their infancy, before they become existential business failures.
For the majority of SMBs, this philosophy breaks down into five main practice categories.
- 24/7/365 monitoring
- Threat Detection
- Response
- Remediation
- Backup recovery and data reinstation
Note: IT security best practices do not mean avoiding all breaches or attacks. That is an impossible goal, one likely to result in cyber-fatigue. Likewise, a small business’ security checklist can’t implement everything at once, even if strategic goal alignment and enterprise resources are there. That, too, leads to IT employee burnout and the increased chance of skipped or forgotten best practices.
Talk to a Cybersecurity Expert
Business Risk of Not Instituting a Cyber Security Checklist
There is a myriad of risks organizations expose themselves to without diligent IT infrastructure security.

1. Financial Loss
Nearly 47 percent of cybersecurity breaches will end up costing a business around $500,000 to remedy. What’s more, cybersecurity incidents force one out of every two SMBs to permanently close its doors, the financial toll too steep to overcome.
2. Operational Halts
Security breaches can shut down “business as usual” while teams and IT departments scramble to mitigate the damage. From receiving a security alert to manually reviewing, escalating and addressing its source, turnaround times for business IT security can be a few hours to a few weeks, depending on the severity and type of cyberattack. Can your business afford to halt operations that long?
3. Lost Customers and Clients
Seven out of 10 consumers say they would stop doing business with a company that misused or under-protected their data. With the recent — and significant — user data mismanagement examples of major organizations like Facebook and Equifax, businesses today must prove their customers’ data is a priority, not an afterthought. Neglecting to do so risks losing your very customer base.
4. Culpability With Investors and Shareholders
Companies must balance consumer trust as well as stakeholder trust. A cybersecurity incident can shake stakeholders’ confidence, with investors, shareholders, partners and any other parties that hold a vested interest in the company’s future needing assurance that IT infrastructure does indeed uphold contemporary best practices.
5. Damaged Reputation
Operational disruptions, investor dissatisfaction and loss of customer trust will ultimately take a toll on a brand’s perception. Cybersecurity negligence defines, if not taints, company reputations. It can take years — and massive PR work — to overcome the negative perceptions and turn a new branding chapter.
6. Regulatory Retaliation
Depending on the scope of a cybersecurity breach and the industry your organization is in, network security negligence can open the doors to regulatory fines. If they are severe enough, government agencies may even press for legal repercussions for culpable parties.
Guide to Small Business IT Security
What should be on an IT infrastructure security checklist for SMBs — or any-sized organization seeking bolstered network security management? We’ve outlined practical, actionable suggestions for sharpened business network security.
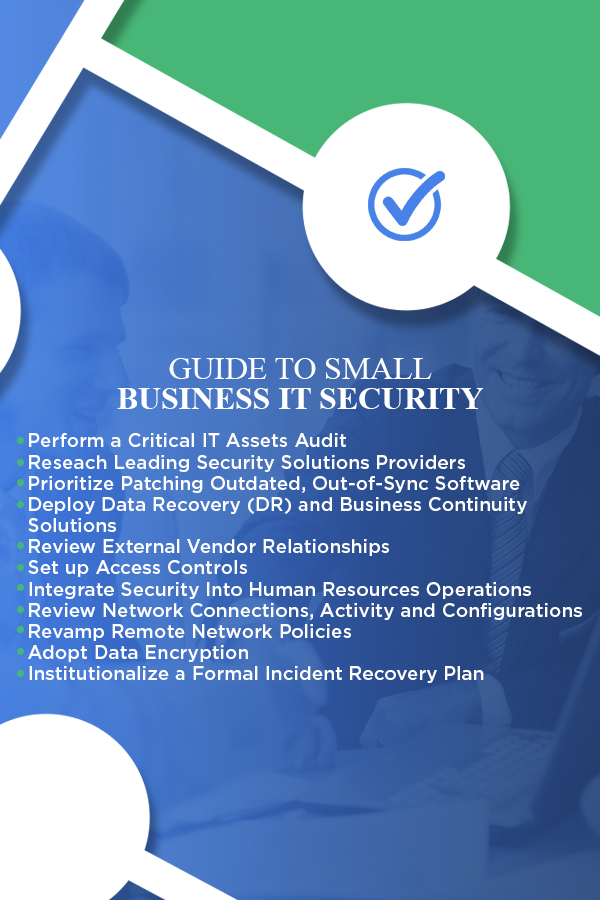
1. Perform a Critical IT Assets Audit
Before any official security checklist can be drafted, SMBs must first take inventory of its most critical IT assets. This includes analyzing its:
- People: The knowledgeable and dedicated staff that makes up all the teams and domains of your IT department, as well as who those teams report to within the larger organizational structure.
- Processes: The daily roles, procedures, responsibilities and initiatives helmed by your IT personnel and utilized by all across the SMB.
- Technology: The physical infrastructure of your network ecosystem, accounting for all pieces of hardware, software, storage methodologies, files, applications and more.
Performing an IT asset audit presents visibility over your business’ entire IT environment. It leaves no stone unturned, providing a guiding compass that’ll steer your ultimate security best practices checklist.
2. Research Leading Security Solutions Providers
Researching industry security leaders is the second step for SMBs and other organizations to begin their network and IT security checklist. Organizations will use their critical IT asset audit to begin vetting security partners with products and services fitting their exact needs.
Today, companies like Cisco make and manufacture leading networking hardware, software, tech security systems and other products related to enterprise IT infrastructure. By partnering with a comprehensive computer networking partner, like Cisco, SMBs can consolidate their security support through a single, convenient vendor — so long as that vendor delivers the range of security mechanisms required of their critical assets.
In other words, partnering with a leading security solution provider like Cisco provides a “one-stop security shop” for business network security, offering products like:
- Advanced malware protection
- Advanced firewall defenses
- Phishing, spoofing and ransomware business email security
- A central breach alert system
- Network visibility and segmentation features
- Secure remote network access solutions
- Multi-factor authentification technology
- Cloud security solutions
- And more
3. Prioritize Patching Outdated, Out-of-Sync Software
Infrequently updated operating systems and software create vulnerabilities across an SMB’s IT mechanisms. This incongruent patchwork stack is ripe for attackers, who can write code to exploit vulnerabilities when devices are not routinely kept up to date.
For software and desktop security, ensure your business network security checklist contains:
- Audits that inventory all operating systems and versions used in your business — including those that enter your network through BYOD — as well as their physical hardware, locations and IP addresses. The goal in these audits should be to consolidate the number of operating systems and shadow IT in use.
- Operating system reviews, ensuring you’re using the latest version to remove bugs and vulnerabilities
- Regularly updated, dynamic anti-virus software
- Contemporary security controls in your firewalls and routers
- Frequently refreshed, effective email filters defending employees against spam, phishing and malware
4. Deploy Data Recovery (DR) and Business Continuity Solutions
Regularly backing up enterprise data is an SMB IT best practice, yet over half of SMBs admit they are unprepared for even a minor data-loss incident, from hard-drive malfunctions to an outsider breach.
Whether cloud-based, on-premise or both, data recovery should include standardized efforts like:
- Regularly performed recovery tests.
- Weekly tested backup systems.
- Data categorize into business-critical or strategic, then backed up accordingly. Business-critical data pertains to any information required to keep daily operations running, whereas strategic data is essential to the enterprise as a whole but not accessed or updated daily. It is an industry best practice to have three backup systems for business-critical data, one centralized on site and one backed up remotely every night. Plan semi-regular backups for strategic data.
- Off-premise data backup, either into the cloud or onto external hard drives not permanently connected to the devices they back.
5. Review External Vendor Relationships
From sourcing raw materials to hiring contractors to maintaining utility contracts, third-party services are a fundamental part of a fully functioning modern business. They’re inevitable, not extraneous.
However, a growing body of research indicates SMBs with fewer external vendors experience fewer security alerts, meaning reduced instances of perceived network threats or inappropriate access. Over half — 63 percent — of organizations with one to five vendors saw fewer than 5,000 alerts a year, as well as remediated 42 percent of those alerts on their own. Only 42 percent of organizations with five to 10 external vendors cited the same alert-remediation flows, indicating that streamlining vendors is an IT network best practice for organizations to consider seriously.
6. Set up Access Controls
Network access controls tier what programs and applications employees can log into, as well as when and how. Employees with “normal” user privileges can only access fundamental programs and must go through a multi-verification approval process for others. Those with “advanced” user privileges can use a broader range of applications while undergoing continuous security training.
Access control best practices include:
- Setting up unique, single-employee user accounts for all systems, programs and apps — never shared accounts
- Installing a central login management program, which tracks and logs all program user history
- Using only one remote-access portal or program, tightening endpoint security for remote or out-of-office workers
- Automated monitoring of user server use, flagging strange or irregular usage for manual review — g., logins outside of business hours
7. Integrate Security Into Human Resources Operations
Human resources departments can be powerful defenders of your small business network security checklist. Their daily touchpoints with current employees, as well as onboarding and interactions with new and prospective ones, positions them as a critical resource to instill safer technology users throughout the office.
Too often, IT security remains the siloed responsibility of the IT department. While this is understandable, there are many ways HR operations can bolster technical infrastructure with safer human protocols.
- Draft and maintain an acceptable use policy for office hardware, including desktops, laptops, smartphones and telecom devices.
- Draft and maintain explicit confidentiality agreements between third-party vendors, freelancers and contractors.
- Draft and maintain best-practice password rules and procedures. At the bare minimum, employees should be updating passwords every 90 days.
- Implement mandatory two-factor authentification for certain program logins beyond simple usernames and passwords.
- Create overall network privacy policies for employees to sign.
8. Review Network Connections, Activity and Configurations
Threat detection begins with basic network monitoring capabilities. SMBs — and businesses of any size — must deploy technology allowing connection activities across all servers, maintaining a clear view into who’s on your network, where they’re accessing it from, when and even why.
- Review all current network configurations, meaning the connections between business hardware, software and operating systems. Ensure each has a static IP address, a dedicated domain name server (DNS) and even a WINS name if using Windows.
- Instate an official BYOD policy. Have employees register those devices with your DNS list using out-of-band management best practices.
- Conduct training on proper email and communications activities, especially to help employees identify spam, malware and more business network threats.
- Outline acceptable device use and internet access policies.
9. Revamp Remote Network Policies
Better control of remote endpoints is growing more and more critical for today’s SMBs. Whether those endpoints are freelancers working from home, customers ordering online or third-party vendors interfacing with some aspect of your internal network, businesses now court more entry points for malicious cyber-activity.
Luckily, as the need for tighter remote network controls and access has increased, so have the defenses:
- Use a set virtual private network for remote employee access.
- Employ LAN or wireless LAN authentication technology — Cisco’s Wireless Security Suite — to allow only approved devices to connect to your wireless internet.
- Install firewall intrusion detection software for all web connections and portals.
- Compile secured wireless access connections and modems into your DNS list, ensuring no unauthorized connections pop up.
10. Adopt Data Encryption
Data encryption works by translating stored plaintext information into a new pattern, called ciphertext, according to an encryption key. Only people who have the key can unscramble the data, adding an extra layer of defense against data thieves.
Data encryption is particularly important to protect customer information. Not only is there a growing movement for tighter regulations of consumer PII, but companies have their very reputation to protect when guarding sensitive data, such as:
- Customer financial information, like credit, debit cards and bank accounts
- Social Security numbers
- Medical history
- Intellectual property or confidential business data
- Financial reports
11. Institutionalize a Formal Incident Recovery Plan
As a final security measure, businesses must establish an intra- and inter-department plan in the event of a major cybersecurity incident. These are known as incident response and recovery plans, and they are a keen indication of the stability of a business’ overall IT infrastructure management — plus its continuity abilities when incidents do strike.
Response and recovery plans should be fully integrated across systems. The best include continual plan audits, complemented by frequent vulnerability tests aiming to identify systems backdoors and weaknesses well before outsiders can.
Learn More About IT Security Managed Services for Your Small Business
Morefield Communications has been arming best-of-class IT solutions across client networks, IT support, IP telephone systems and premise security for decades. We partner with some of the world’s leading network security providers to bring businesses — like yours — peace of mind.
Reach out online or give us a call at (717) 761-6170 to create your business’ IT security checklist today.

The Top 5 IT Challenges Facing Manufacturers and How to Overcome Them

Manufacturing is at the heart of any thriving economy, and the current economic environment pushes manufacturers to create a more digital and data-driven workforce. Manufacturing is a vital industry, and it’s no surprise that IT challenges continue to keep manufacturers vigilant. Manufacturing companies face a unique set of IT challenges.
From data migrations and cybersecurity breaches to workforce automation and machine learning, manufacturers’ challenges are vast and varied. However, competing as a manufacturer in an increasingly global market may be challenging. Adopting new technology is one strategy to gain an advantage and maintain market share. But what other strategies are there for these manufacturing IT challenges?
Challenge #1: Increasing Cybersecurity
With the increased usage of technical improvements, manufacturing business owners must be aware that cyberattackers mainly target their businesses. In 2021, the manufacturing industry experienced over 23% of total cyberattacks worldwide. The manufacturing sector experienced the highest share of cyberattacks — more than the finance and insurance sectors.
Furthermore, the Engineering Employers’ Federation (EEF) states that more than 45% of manufacturing businesses have experienced cybersecurity problems. The first step toward developing a cybersecurity solution is learning about commonly used cyberattacks in the manufacturing industry:
- Phishing attacks: This attack occurs via malicious email attachments or targets visiting fake websites, corrupting browser settings and using business data for financial gain. A virus discovers vulnerabilities in systems and sends information to attackers.
- Ransomware: This software encrypts files on a network and renders them inoperable until hackers’ demands are satisfied. These attackers may threaten to sell or disclose essential data if a ransom is not paid. Ransomware also renders the company’s network inoperable. Downtime places such a hardship on manufacturing organizations, making this strategy highly successful.
- Supply chain attacks: This attack damages one link in a company’s supply chain that can have massive repercussions. Hackers can access big corporations through weak points in their partners’ and suppliers’ systems. These attacks are double-edged swords. If a major firm is forced to shut down operations, any company it supplies is equally impacted within days of the first attack.
- IP theft: Manufacturing companies own intellectual property (IP) that distinguishes their products or services. As attackers discover new techniques to infiltrate a network undetected, the risks of possible IP theft increase. Hackers can silently harvest the required information and exit the system undiscovered. This might result in stolen or changed data.
The following techniques can help companies become more aware of potential hazards, identify possibly harmful conduct and avoid manufacturing IT cybersecurity problems:
- Educate all personnel about the dangers of cybercrime and how to identify possible threats.
- Implement password policies that require strong passwords and two-factor authentication where possible.
- Apply all updates and patches for relevant software as soon as they become available.
- Updated methods to manage backups of company data.
- Inform staff about the risks of accessing attachments from unknown sources.
Challenge #2: Integration of New Technologies
Smart manufacturing uses internet-connected technology to track the manufacturing process. This enables machines to interact with one another through the internet and collaborate to reduce mistakes and enhance plant workflow. Smart manufacturing also aids in the identification of better prospects for automated operations and the use of data analytics to improve and optimize the overall production process.
Some current technologies and solutions in the smart manufacturing environment include automation and robots, predictive analytics and artificial intelligence (AI). Manufacturers must be innovative in incorporating new technology to flourish in increasingly competitive markets. This is quite a challenge due to the rate at which technology continuously advances.
The Internet of Things (IoT) is another challenge on its own. Manufacturing hardware is increasingly being linked to the internet. However, these technologies are particularly prone to hackers. Networks must be configured to be functional, reliable and secure to keep IoT devices safe.
Here are a few strategies a company can implement to overcome these manufacturing IT problems:
- Research and testing: Strive to do thorough research and testing on new technologies that can improve manufacturing processes. Each company is different and requires specific AI software or robotics that suits its needs. Performing proper tests and evaluating the collaboration between these new technologies and existing operations are crucial to its successful implementation.
- Work with partners: To overcome the various challenges, working with experienced partners in the industry is best. They may provide valuable insights into successfully integrating new technologies, especially in the manufacturing industry.
- Provide employee training: Businesses must include their employees and make change management simple for them if they want to enhance the manufacturing process through new technologies. One approach is to provide a consolidated location for information that offers continuous employee training through videos, manuals and other training materials together with standard operating procedures (SOPs).
Challenge #3: Managing Data and Analytics
Manufacturers may find it challenging to analyze their data to develop insights. Today’s technology platforms constantly generate data on supply networks, manufacturing lines and employee performances. Massive volumes of data are available to manufacturers.
Forecasting product demand and inventory management are two major areas where data analysis may be beneficial. External factors influence product demand, such as currency exchange rates, current market trends and supply chain pricing. To maximize manufacturing, data from various sources must be readily available, accurately collected and stored and well managed.
Companies can start overcoming these IT challenges in manufacturing by following these strategies:
- Implement a DMS: Implementing a robust data management system (DMS) will help the manufacturer’s overall data accessibility and management. Manufacturers can define their infrastructure strategy, choose their data collection method and keep everything organized and optimized.
- Data analysis training: Training personnel on data analysis is a valuable skill that can benefit the firm. Data analytics is a science and an art. It’s a complex field where some businesses need to hire specialists. Providing data analysis training to employees may help them better understand the intricacies of data.
- Partnering with experts: Partnering with data experts helps manufacturers analyze, design, facilitate and complete duties associated with developing their data and information architecture. Experts provide reusable standards, rules, design patterns and settings to evolve data and information infrastructure across whole companies.
Challenge #4: Maintaining Uptime
This is an age-old manufacturing IT dilemma. Downtime, particularly unscheduled downtime, is detrimental to profits. The average hourly cost of server downtime worldwide was between $301,000 and $400,000 in 2020. There’s no doubt that unexpected downtime is expensive. It remains an ongoing and severe problem regardless of the precise cost per industry. IT system reliability is critical to avoiding downtime.
Try to implement a few other strategies to handle these manufacturing IT challenges:
- Perform routine maintenance: Maintain your systems regularly to keep them operating at their best. This involves scheduling scans and deploying security fixes in your IT infrastructure to address software vulnerabilities before hacks occur.
- Plan ahead: Prepare a plan and a timetable for system upgrades to keep hardware and software up to date.
- Test backups: Develop backup and restoration procedures with the appropriate resources and test them regularly to ensure flawless business continuity. Testing your backups can provide you peace of mind that you can restore your data in an emergency.
Challenge #5: Staying Competitive in a Rapidly Changing Market
Being in the manufacturing industry today requires companies to be agile to stay competitive in a rapidly changing market due to the growing rate of technological development. Manufacturers must be able to react to shifting market needs and technological advancements swiftly. This is challenging since conventional manufacturing lines were frequently highly tailored for specific applications.
Integrating older systems with cutting-edge applications and platforms to increase production quality and efficiency can be challenging. It can also be difficult to develop production processes that can adjust fast as data changes.
Some strategies to overcome these challenges include the following:
- Stay up-to-date: Staying updated with the most recent market trends and adopting new technology can provide a competitive advantage over the competition. A business owner who can successfully understand and apply the most recent technological advancements can stay ahead of the competition.
- Invest in research and development: To stay up-to-date with the latest news, trends and developments, manufacturers must invest in proper research and development of new technological advancements.
- Remain adaptable: From research and planning comes action. Manufacturers must remain agile and adaptable to changes in the industry — specifically if they can benefit from it. Change is unavoidable.
Outsource Your IT Support With Morefield
Position your manufacturing firm ahead of its competition and implement strategies that overcome these top five IT challenges. Businesses may only function with proper IT assistance, making the selection of IT service providers critical. Outsourcing your IT support may be more cost-effective than building an in-house IT team from scratch.
Morefield is a leading provider of corporate technology solutions. We assist enterprises in integrating and improving their technologies, streamlining their corporate technology with unmatched customer care. Our professionals will build and maintain every aspect of your network for integrated solutions that maximize productivity in your business.
Contact us online, and we’ll respond to your request promptly.
2023 Trends in Data Privacy That Could Impact Your Compliance
Data privacy has been a growing requirement ever since the internet age began. So much personal information is flying around through computer networks. Protecting it has become a mandate.
Most companies must follow HIPAA, GDPR, or another industry or locality-based privacy rule. By the end of 2024, 75% of the world’s population will have their personal data protected. It will fall under one or more privacy regulations. You don’t need to be a large enterprise organization to have data privacy compliance at the top of your mind. It goes hand in hand with cybersecurity. Additionally, privacy requirements hit all sized companies. Between July 2020 and July 2021, GDPR violations rose by 113.5%. The number of associated fines also jumped, by 124.92%. When it comes to HIPAA violations, each incident can carry a penalty between $100 to $25,000. It’s important to make data privacy a priority and factor it into all your data collection processes. When companies collect, send, or store personally identifiable information (PII) it needs protection. This means putting adequate safeguards in place. To stay on top of your privacy compliance obligations, you should also keep up with trends in this area. Next up, we’ve documented the biggest data privacy trends happening in 2023 that you should be aware of.
What’s Happening in Data Privacy Compliance?
AI Governance 
Approximately 40% of privacy compliance technology needs artificial intelligence (AI) to operate. AI has certainly made its way into many of the applications we use on a daily basis. When you’re typing in MS Word and text just springs up as a suggestion, that’s AI predicting what you’ll type next. When working on a photograph in Photoshop, you can now click a button to give a frowning face a smile. This is also the work of AI.
So, it’s no surprise that AI is running many of the algorithms responsible for keeping data protected. But what happens when there is a problem with the AI? This is the question that AI governance is working to address. This is a new trend in data privacy because AI has never been so prevalent throughout the data journey as it is now. Whenever AI is used in the data protection area, organizations need to govern it properly. This helps ensure that automated processes aren’t accidentally exposing sensitive data.
Consumer Privacy UX
A trend that we’ve seen over the last several months is putting more privacy power into the consumer’s hands. Many privacy regulations require that apps and websites provide data transparency. They need to tell people what data they’re collecting, how they’re collecting it, and what they do with it. People also need an “out” to get their data back. These needs have led to consumer privacy UX becoming a “thing.” You can think of this as a centralized privacy portal. A place people can access privacy-related settings in various apps. This gives better visibility into how their data is being used.
Increased Scrutiny of Remote Employee Monitoring
The pandemic has forever changed the global workforce. Many organizations are now running completely remote offices. Or may be using a mix of remote and in-office staff. The dramatic increase in people working from home has led to data collection changes. Companies are ramping up their monitoring of those employees working off-site. But this type of monitoring opens a can of worms when it comes to data privacy. Organizations need to ensure that they aren’t encroaching on the rights of their staff. This is most pertinent when putting monitoring in place on employee devices. For example, approximately 49% of remote employees use their personal computers for work. Companies often put endpoint device monitoring in place for security reasons. They need to ensure they are not gathering or backing up any personal data. That would be data owned by the employee and not the company.
Data Localization
One of the concerns when the social app TikTok became popular relates to location. With the firm being a China-based company, people worried about the privacy of their data. The data was originally stored on servers governed by the Chinese government. A country with very different data privacy rules than the US and other countries. Data localization is going to become more prevalent. Increasingly organizations look at where their cloud data is being stored. Where a server resides governs the privacy rules and regulations that it may fall under. Thus, companies and governments are now asking a question of cloud providers. This is, “Where is my data stored?” Many want their data to be as close to home as possible.
Privacy-Enhancing Computation (PEC)
Data privacy by design is a fairly new term. Using privacy-enhancing computation is a way that AI is helping cybersecurity. By using PEC as a built-in component of software and apps, developers provide value to clients. They address privacy concerns by making data protection more automated. Look for PEC components in data analytics when shopping for business tools.
When Is the Last Time You Had a Compliance Check?
How are your data privacy protections? Are you risking a penalty due to lax controls? Give us a call! We can help with a compliance checkup.
Article used with permission from The Technology Press.


